Category: Purple Team
-
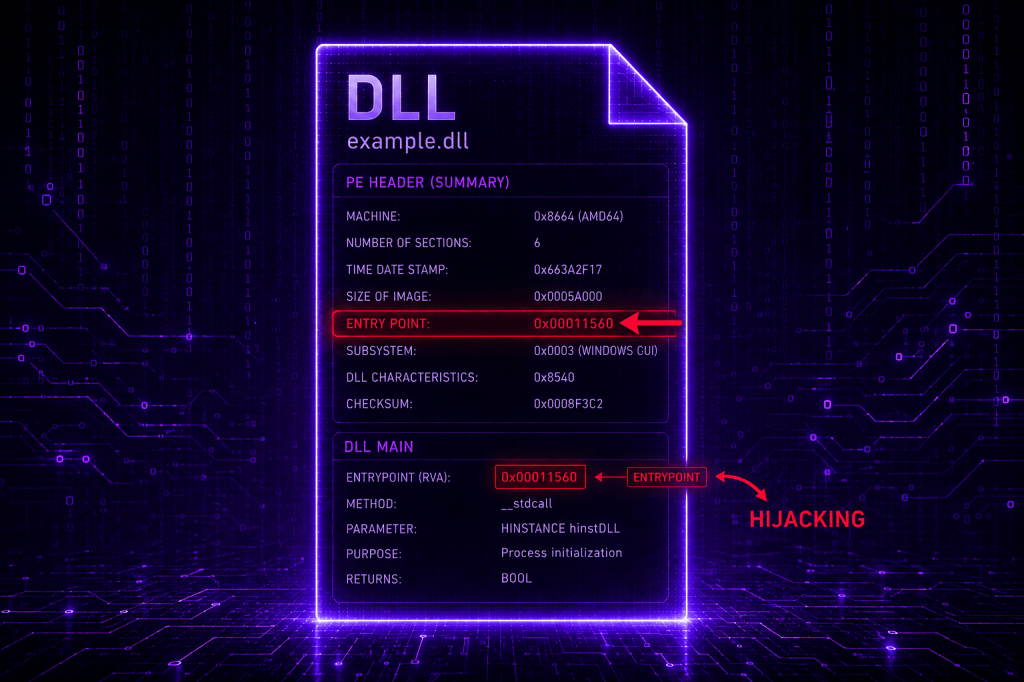
EntryPoint Hijacking
The technique of EntryPoint Hijacking introduces a stealthier approach to code injection, as it doesn’t rely on API calls that create a new thread within the process context, and it is independent of the attack chain. Arbitrary code is written to memory, but it executes only when the process legitimately…
-
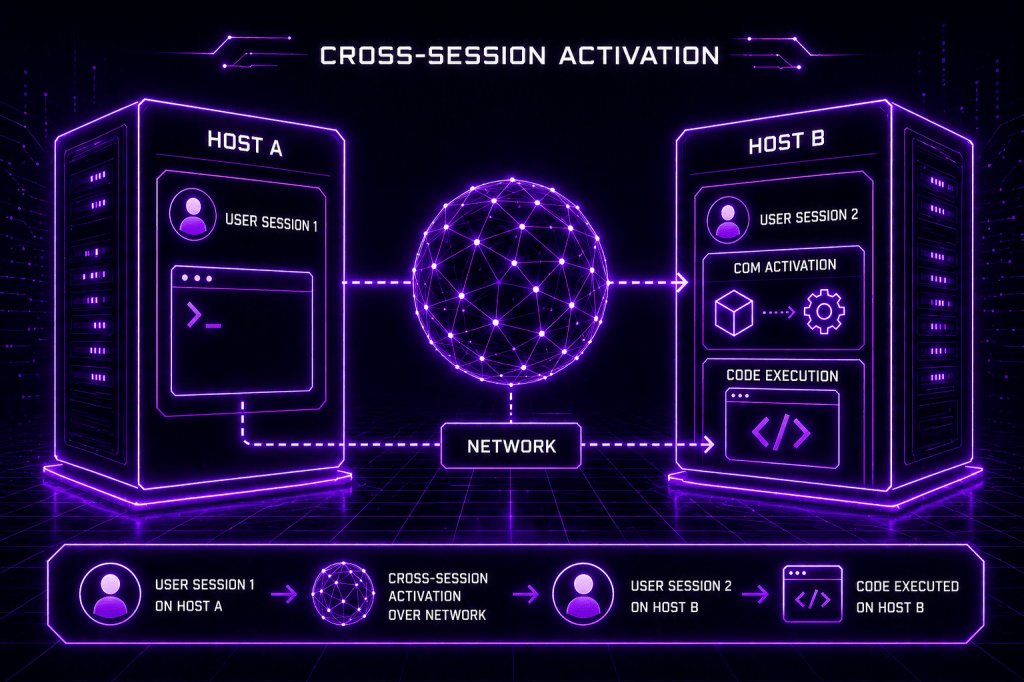
Cross-Session Activation
Traditional lateral movement techniques are no longer applicable in the modern era due to developments in the detection capability by most of the EDR vendors. Techniques that abuse legitimate Windows functionality, such as COM, has always been in the interest of adversaries. Cross-Session activation (CSA) is considered the latest evolution…
-

Microsoft Speech
SpeechRuntime is a legitimate Windows component that supports Microsoft’s speech-related capabilities, including voice input and speech recognition features used across modern Windows experiences. The SpeechRuntime.exe binary is linked to the Microsoft speech framework. However, threat actors with elevated privileges can move laterally by executing code under the context of the…
-
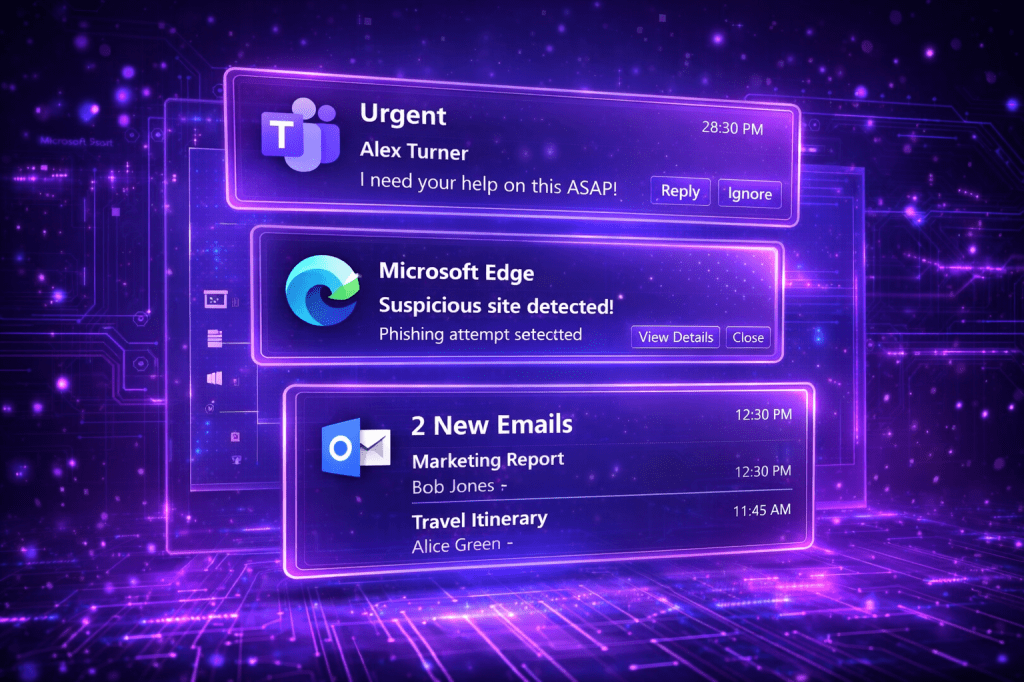
Toast Notifications
The Application User Model ID (AUMID) is a unique identifier that Windows assigns to modern applications. It enables Windows to identify which applications should receive notifications, how start menu entries are associated, how toast notifications map back to an application etc. Many organizations use Toast Notifications to push internal updates…
